CCleaner is a popular and powerful PC tool that helps users to clean up their PCs by deleting temporary files, emptying recycle bins, deleting registry leftovers after program uninstall, etc. The free version is at the top of the popular software list on FileHippo.com. On September 13, 2017, Cisco’s Talos cybersecurity reported that CCleaner has been distributed with malware for almost one month, and the infected version is the 32-bit version of CCleaner 5.33 which was released on August 15 and the 32-bit version of CCleaner Cloud 1.07.3191 released on August 24. Piriform, the company developed CCleaner, announced the security issue today, but interestingly without giving any credits to Cisco’s Talos team. Their release announcement and blog post seem to indicate that Piriform detected the malware themselves on September 12, 2017. My request for comment on this from Cisco’s Talos team has not been responded and I will update this post once I receive a response.
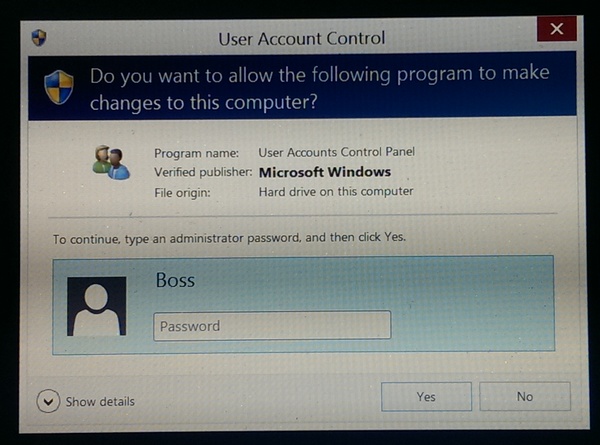
People think the malware was injected by hackers, but I don’t believe it is the case. I truly believe it is an inside job. Hear me out.
When you download the free version of CCleaner, you will be provided with a checksum, after you download the software you will generate another checksum from the downloaded softare, if the two checksums don’t match, that means the downloaded software has been tampered and you shouldn’t install it. However, no one reported the corrupted checksum, that means the malware was not injected after the binary executable was created. The only explanation is the malware was injected during the development phase or the signing process of the software. If hackers got the access to that level, then they should have done something more lucrative then injecting malware, that is the first reason I believe it is not from hackers.
My second reason is that CCleaner was acquired by Avast, a leading anti-virus company from Czech Republic, in July 2017, and one month later a malware-injected version was released and distributed from Avast server. I suspect some CCleaner developer(s) is/are not happy with the acquisition and secretly inject the malware to tarnish the reputation of CCleaner. Don’t you think the timeline is very suspicious?
If Cisco Talos was the first detected and reported the malware, that it is very ironic that the leading anti-virus company Avast didn’t detect the malware in their own product, maybe it is the real reason the malware was injected in the first place.
You should check your version of CCleaner, if yours is infected, then you will need to download a removal tool to remove the malware, then update CCleaner to the latest version, according to the Talos team.
What does the malware do anyway?
When you launched the infected version of CCleaner, the malware will profile your system and then try to send the collected information to an external server. Once the connection between the infected and the external server is established, a second-stage payload will be downloaded and be executed. Fortunately, according to both Cisco Talos and Piriform, the second-stage payload does not seem to be activated yet (hackers left something important unfinished? Really?) In case the connection between the infected computer and the external server cannot be established, the malware will try to use Domain Name Generator to redirect the traffic to a different location. Again, fortunately “the generated domains are not under the control of the attacker and does not pose any risk”, according to Piriform (do you still think this is a hacker’s job?)
If you are curious, the following flowchart shows how the malware is launched and does its dirty work.